Wireguard is a next-generation open-source VPN connection protocol that claims to be faster and more secure than Open-VPN.
In this tutorial we will cover how to setup and configure a WireGuard VPN Server on a Debian Linux Distribution as well as how to get a Windows machine to route all traffic through that VPN using WireGuard’s Windows Client.
Step 0 : Install Un-Attended Updates
First, lets ensure we setup automated updates as we will want security patches and its likely that we wont be touching this VPS for a while.
apt-get install sudo sudo apt-get install aptitude sudo apt-get update && sudo apt-get upgrade sudo aptitude update -y && sudo aptitude install unattended-upgrades apt-listchanges -y sudo dpkg-reconfigure -plow unattended-upgrades
Step 1 : Install WireGuard and Generate Keys
First lets edit our sources
sudo nano /etc/apt/sources.list.d/unstable.list
add the following line
deb http://deb.debian.org/debian/ unstable main
Open
sudo nano /etc/apt/preferences.d/limit-unstable
add the following lines
Package: * Pin: release a=unstable Pin-Priority: 150
Update your package lists and install WireGuard
sudo apt update sudo apt install wireguard
Check that its loaded
lsmod | grep wireguard
Now lets ensure that IPv4 Forwarding is enabled
sudo nano /etc/sysctl.conf
Uncoment the following
net.ipv4.ip_forward=1
Now to save we need to
sudo sysctl -p
Now its time to generate your VPN’s private key
KEYS PROVIDED HERE ARE JUST EXAMPLES, DO NOT USE THEM AS THEY ARE PUBLIC AND INSECURE NOW
wg genkey
It’s important to write this down somewhere safe and private it’ll look something like this
uDXR7FnTzGarLNj+E3ePv4gOwsbjumZ7M9YjcKAQ8WI=
Now its time to generate the corresponding VPN’s public key using the private key we just generated
echo "uDXR7FnTzGarLNj+E3ePv4gOwsbjumZ7M9YjcKAQ8WI=" | wg pubkey
It’ll look something like this, write it down somewhere
9XIklpw4lGQ/I0S9L3gqTjwjJYsXJPluihomcCCrEzU=
Now its time to generate the User’s private and public key pair, note you will one for each user of the VPN (this essentially the same process as before)
wg genkey
Write down the User’s private key somewhere safe
0IoyeQyyWPYVGf4P4DosBGHHrl/T7k+2fqFc8JZRmGo=
Now lets generate the User’s public key
echo "0IoyeQyyWPYVGf4P4DosBGHHrl/T7k+2fqFc8JZRmGo=" | wg pubkey
Write this down somewhere
JoYcG0Bq5+dMrEAc8eSTG6QCFBjwUWxfXTy7LWmhC0k=
Step 2 : Configuration of WireGuard Server
First we need to find our active interface
ip l
Will show something like
1: lo: mtu 65536 qdisc noqueue state UNKNOWN mode DEFAULT group default qlen 1
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
2: eth0: mtu 1500 qdisc pfifo_fast state UP mode DEFAULT group default qlen 1000
link/ether 53:55:00:91:36:5c brd ff:ff:ff:ff:ff:ff
Here eth0 is our interface, now lets check our public IP address
ip a show dev eth0
2: eth0: mtu 1500 qdisc pfifo_fast state UP group default qlen 1000
link/ether 53:55:00:91:36:5c brd ff:ff:ff:ff:ff:ff
inet 5.1.1.1/24 brd 5.188.238.255 scope global eth0
valid_lft forever preferred_lft forever
inet6 2103:90c0:186::20/48 scope global
valid_lft forever preferred_lft forever
inet6 fe80::5058:ff:fe89:c66d/64 scope link
valid_lft forever preferred_lft forever
So here we can see our public IPv4 address is 5.1.1.1/24
Now lets create our configuration file
sudo nano /etc/wireguard/wg0s.conf
add the following, note where the User’s public/ VPN’s private keys go as well as our public IPv4 address and client’s public IPv4 address
[Interface] Address = 5.1.1.1/24 PostUp = iptables -A FORWARD -i %i -j ACCEPT; iptables -A FORWARD -o %i -j ACCEPT; iptables -t nat -A POSTROUTING -o eth0 -j MASQUERADE PostDown = iptables -D FORWARD -i %i -j ACCEPT; iptables -D FORWARD -o %i -j ACCEPT; iptables -t nat -D POSTROUTING -o eth0 -j MASQUERADEACCEPT; iptables -t nat -D PO$ ListenPort = 8081 PrivateKey = uDXR7FnTzGarLNj+E3ePv4gOwsbjumZ7M9YjcKAQ8WI= [Peer] PublicKey = JoYcG0Bq5+dMrEAc8eSTG6QCFBjwUWxfXTy7LWmhC0k= AllowedIPs = 192.168.1.2/32 PersistentKeepalive = 25
Now lets start it up
sudo wg-quick up wg0s
Check that it is running
wg show
You can terminate it if needed using
sudo wg-quick down wg0s
Step 3 : Setup and Configure Windows 10 WireGuard Client
First lets download and install the WireGuard Windows Client
https://www.wireguard.com/install/
In this tutorial we will be using Windows 10 64 bit so hit the button for downloading that version
Run through the installer and then open up the WireGuard Interface
Click Add Tunnel -> Add Empty Tunnel
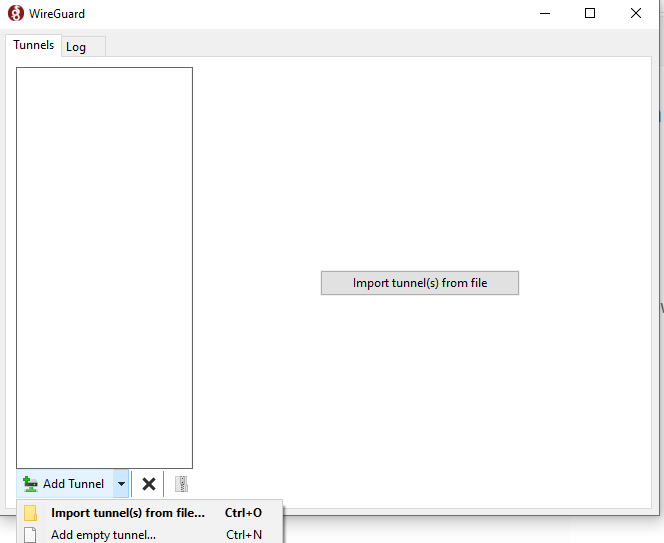
Now add the following in, being careful to swap the keys with yours (note here we are providing the User’s Private Key followed by the VPN’s Public Key, and that the first Address is our local address)
[Interface] Address = 192.168.1.2/24 ListenPort = 50001 PrivateKey = 0IoyeQyyWPYVGf4P4DosBGHHrl/T7k+2fqFc8JZRmGo= [Peer] PublicKey = 9XIklpw4lGQ/I0S9L3gqTjwjJYsXJPluihomcCCrEzU= AllowedIPs = 0.0.0.0/0, ::/0 Endpoint = 5.1.1.1:8081 PersistentKeepalive = 25
Give it a name, Save and Activate
Now to check that it’s working head over to https://www.dnsleaktest.com/ on your Windows 10 machine and you should now see your VPN’s IP Address as if it were your own
NOTE: I’ve yet to get this working myself over the internet, certain ISPs may block this protocol and there may be some bugs yet. This information was compiled from various sources over the internet, use at your own discretion.
Extremely user friendly site. Immense info readily available on couple of clicks.